Exploring Audit Data
Required Role: Auditing Viewer (or Full Administrator)
Viewing Audit Events
- Click the Audits tab. By default, the Audit Events report opens, listing all events that occurred within the last hour, with the most recent at the
top:
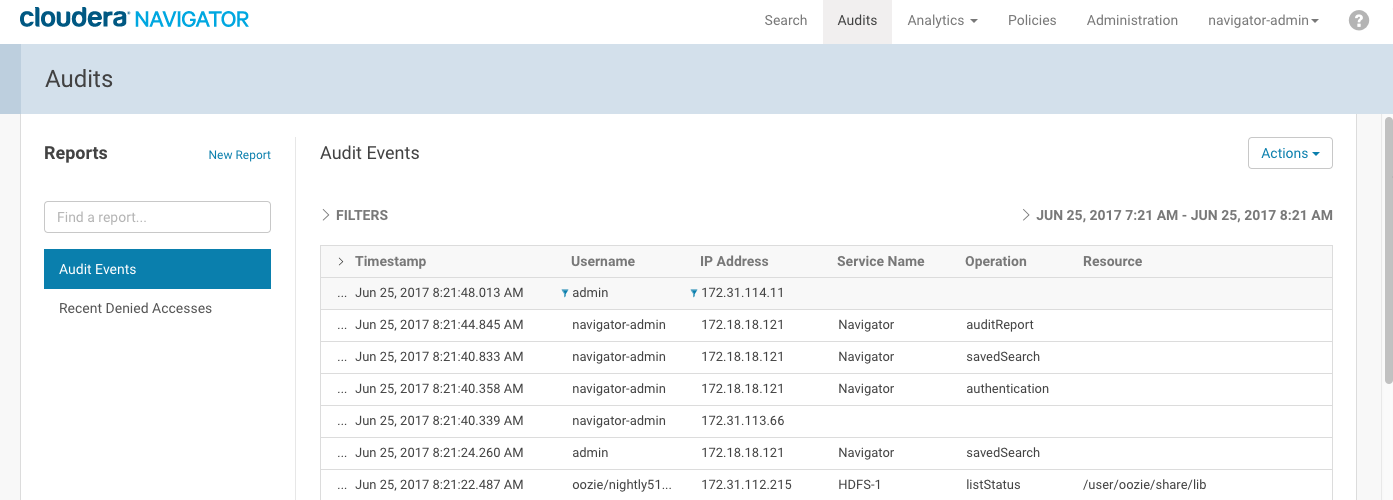
The Audit Events and Recent Denied Accesses reports are available by default. You create your own reports and apply a variety of filters as detailed in the next section.
Filtering Audit Events in the Console
You filter audit events by specifying a time range or adding one or more filters containing an audit event field, operator, and value.
Specifying a Time Range
- Click the date-time range at the top right of the Audits tab to open a range selector.
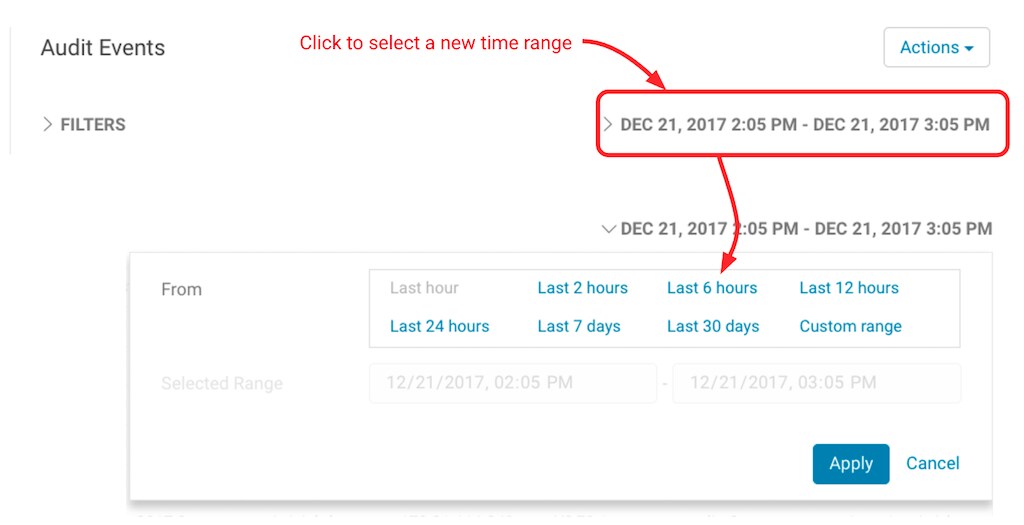
- Select one of the pre-defined ranges.
To enter a specific time range, choose Custom range and use the controls in Selected Range to specify start and end dates and times.
- Click Apply.
Adding a Filter Field
- Click the Filters link.
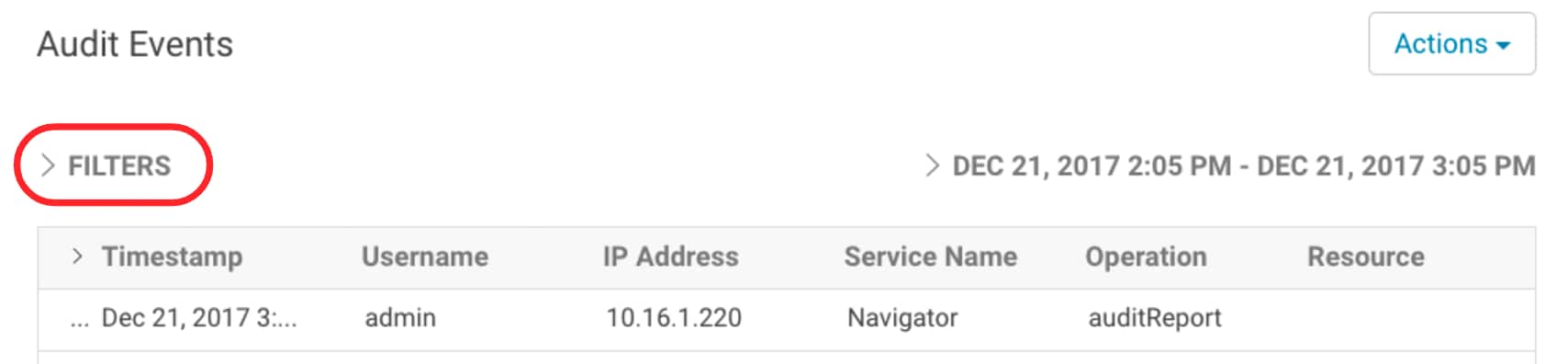
The Filters pane displays.
- Click
 if a filter field is not already open.
if a filter field is not already open. - Choose a field in the Select Property drop-down list.
The properties correspond to the audit fields listed in Service Audit Events.
- Choose an operator in the operator drop-down list.
Choose from = (equals), != (not equals), like, and not like. The like operator matches to substrings. For example, to see all the audit events for files created in the folder /user/joe/out, specify Source like /user/joe/out.
Use not like to filter out events based on a partial string match. For example, to show audit events for a set of IP addresses that start with the same sequence 172.39.109, you can specify IP Address not like 172.39.109. - Type a field value in the value text field.
For example, to see the events listed for Navigator, enter Service Name = Navigator.
- To specify an additional filter, click
 and define the new criteria.
and define the new criteria.
Audit events show that match all filters (AND).
- Click Apply.
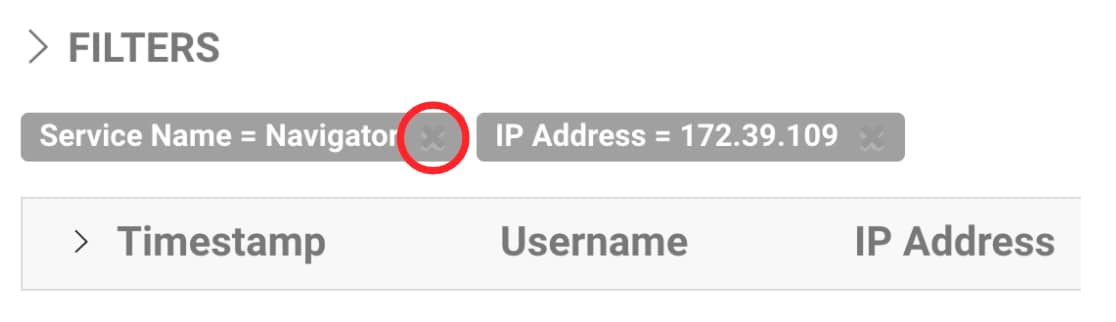
A filter breadcrumb appears above the list of audit events and the list of events displays all events that match all the filter criteria.